CARTP Guide: Runbookadmin, epbackp, HelperAppNewCred_. and iPad Pro Bypass Insights
Working through the CARTP guide (Certified Azure Red Team Professional) labs by Altered Security feels a bit different from typical lab environments. It’s less about chasing obvious vulnerabilities and more about understanding how enterprise systems actually behave under the hood.
At first, names like Runbookadmin, epbackp, and HelperAppNewCred_. might seem like random artifacts. But they’re not. When combined with scenarios like the iPad Pro bypass, they begin to form a much clearer picture of how misconfigurations and assumptions can be abused in real environments.
Let’s walk through this in a more practical, grounded way.
Understanding the CARTP Lab Context
CARTP labs are built around Azure and hybrid enterprise setups. That means automation, identity, and cloud integrations are at the center of everything.
Accounts such as:
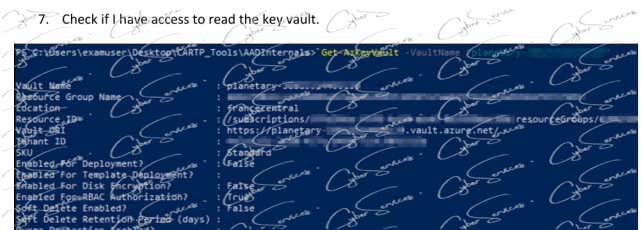
- Runbookadmin
- epbackp
aren’t just users—they represent roles within operational workflows.
And that’s where things get interesting.
Because in many real-world environments, these roles are given just enough privilege to function… but often more than they should have.
Runbookadmin: Automation That Can Be Leveraged CARTP guide
The Runbookadmin account is a strong indicator of Azure Automation usage.
Runbooks are typically used for:
- Scheduled administrative tasks
- Resource management
- Incident response automation
Naturally, they require elevated permissions.
If you come across access tied to Runbookadmin, it’s worth slowing down and asking:
- What automation tasks are configured?
- Are credentials embedded in scripts?
- Can runbooks be modified or executed manually?
Sometimes the real opportunity isn’t direct access—it’s controlling what the automation does next.
epbackp: Backup Access and Hidden Exposure
The epbackp account likely points to backup-related operations.
In enterprise setups, backup systems often:
- Touch multiple critical resources
- Store sensitive configurations
- Operate with broad permissions
That combination makes them valuable.
If this account is accessible, it may allow:
- Reading stored data or snapshots
- Extracting configuration details
- Discovering reused credentials across services
It’s not always obvious at first—but backup-related access can quietly open multiple paths forward.
HelperAppNewCred_.: Temporary Doesn’t Always Mean Temporary CARTP guide
The string HelperAppNewCred_. stands out for a reason. It doesn’t look polished or intentional—it looks like something internal.
That’s usually a good sign.
Names like this often come from:
- Development or testing phases
- Credential rotation processes
- Debugging artifacts left behind
And in many cases, they’re forgotten.
If you encounter it, treat it as a lead:
- Is it referenced in scripts or configs?
- Does it map to an actual credential?
- Is it part of a helper application or service?
Sometimes these “temporary” elements end up being the most reliable entry points.
iPad Pro Bypass: Trust Assumptions in Action CARTP guide
The iPad Pro bypass scenario introduces a different kind of challenge.
Instead of exploiting a technical flaw directly, it focuses on how systems make trust decisions.
In many environments, applications treat certain devices differently:
- Mobile devices may bypass stricter checks
- Specific user agents might be trusted
- Some workflows are simplified for usability
If an application assumes an iPad Pro is a trusted device, that assumption can be manipulated.
Typical approaches involve:
- Adjusting user-agent headers
- Mimicking expected device behavior
- Accessing less-restricted code paths
It’s a subtle technique—but very realistic.
Because in practice, trust assumptions are often where security weakens.
Connecting These Elements in a Real Scenario
Individually, these components might seem unrelated:
- Runbookadmin → automation control
- epbackp → backup access
- HelperAppNewCred_. → credential artifact
- iPad Pro bypass → logic-based access
But CARTP is designed to make you connect them.
A possible flow might look like:
- Using a bypass technique to access restricted functionality
- Discovering configuration data or internal references
- Identifying accounts like Runbookadmin or epbackp
- Leveraging those accounts to expand access
It’s not a straight path—and that’s intentional.
Common Mistakes While Practicing CARTP
It’s easy to overcomplicate things or miss simple clues.
Some common pitfalls include:
- Ignoring unusual strings like HelperAppNewCred_.
- Underestimating automation accounts
- Focusing only on technical exploits while missing logic flaws
- Trying credentials without understanding their context
CARTP labs reward careful observation more than aggressive testing.
A Better Way to Approach It CARTP guide
If progress slows down, try adjusting your approach:
- Re-examine earlier findings with fresh context
- Map each account to its likely role
- Think in terms of workflows, not isolated systems
- Pay attention to naming—it often reflects real usage
And most importantly, don’t overlook logic-based weaknesses. They’re often quieter—but just as impactful.
Final Thoughts
The CARTP certification by Altered Security is valuable because it reflects real-world environments where:
- Automation is widely trusted
- Backup systems have broad access
- Temporary credentials are left behind
- Device-based assumptions introduce risk
Working with elements like Runbookadmin, epbackp, HelperAppNewCred_., and the iPad Pro bypass helps build a mindset that goes beyond tools and techniques.
It teaches you to look at systems the way they’re actually used—and that’s where the real insights are.
Vendor: https://www.alteredsecurity.com/cartp
Buy this dump: https://cyberservices.store/