HTB CJCA Guide: Luminex Ltd. Scenario with TeamCity, ELK01 and Multi-Host Analysis
In the HTB CJCA Luminex analysis (Certified Junior Cybersecurity Analyst) path, things are less about isolated findings and more about understanding how activity spreads across an environment. The Luminex Ltd. scenario is a good example of that.
You’re given multiple systems—Linux, Windows, web services—and a handful of users. On their own, they don’t say much. But once you start correlating logs, access patterns, and behavior, a clearer picture begins to form.
This guide walks through key assets like NIX01, NIX02, WEB01, WIN01, WIN02, alongside services such as TeamCity and ELK01, and users like john, marc, cameron, sfisher, melissajenkins, kimkiara, and the teamcity account.
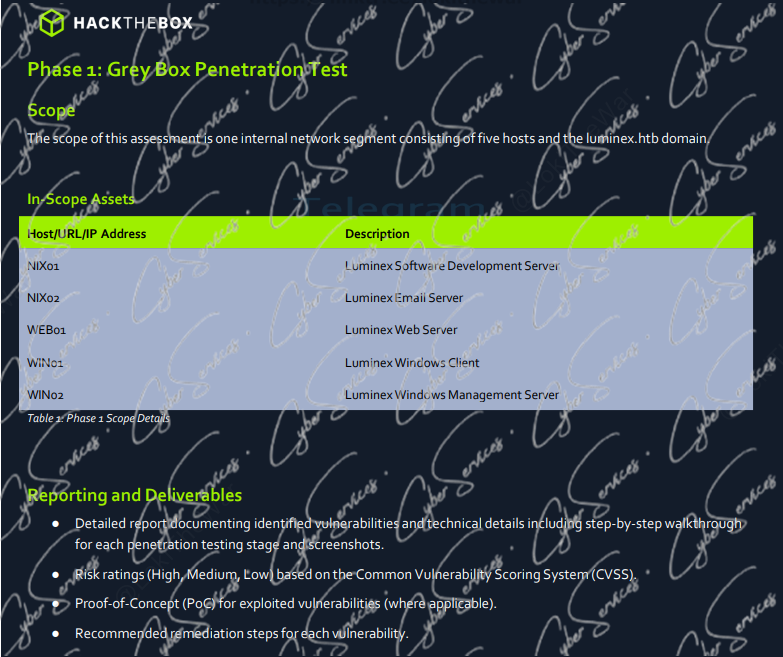
Environment Overview: Luminex Ltd. Infrastructure
The Luminex Ltd. network is structured to simulate a small but realistic corporate setup:
- 10.129.156.46 (NIX01) → Linux system (likely internal services or tooling)
- 10.129.156.47 (NIX02) → Secondary Linux host
- 10.129.156.45 (WEB01) → Public-facing web server
- 10.129.156.44 (WIN01) → Windows workstation/server
- 10.129.156.43 (WIN02) → Additional Windows endpoint
Supporting services:
- TeamCity → CI/CD platform (often high-value target)
- ELK01 → Logging and monitoring stack (Elasticsearch, Logstash, Kibana)
This setup already tells you something important: visibility exists (ELK), but so do potential attack paths (TeamCity, web server, user endpoints).
Starting Point: WEB01 and External Exposure HTB CJCA Luminex analysis
Most investigations naturally begin with WEB01 (10.129.156.45).
Public-facing systems are:
- More exposed
- Frequently targeted
- Common entry points
From a SOC or analyst perspective, you’d look for:
- Unusual HTTP requests
- Suspicious parameters
- Upload or execution attempts
Even small anomalies here can indicate the beginning of a larger chain.
TeamCity: A High-Value Target
The presence of TeamCity is significant.
CI/CD systems often:
- Store credentials
- Execute scripts on multiple hosts
- Have integration access across environments
The teamcity user account is particularly important. If compromised, it could:
- Trigger builds
- Execute commands on connected systems
- Access stored secrets
In logs, watch for:
- Unexpected login times
- New or modified build configurations
- Script execution anomalies
This isn’t just another service—it can become a central pivot point.
User Landscape: Who Matters and Why HTB CJCA Luminex analysis
The Luminex scenario includes several users:
- john
- marc
- cameron
- sfisher
- melissajenkins
- kimkiara
- teamcity
At first glance, they seem like standard corporate users. But in practice:
- Some may interact with WEB01
- Others might have access to NIX systems
- A few could be tied to TeamCity pipelines
The goal isn’t to analyze them individually—but to see:
➡️ where their activity overlaps with suspicious events
For example:
- A normal user suddenly interacting with TeamCity
- Login attempts across multiple hosts
- Access from unusual IPs
That’s where things start to stand out.
NIX01 & NIX02: Internal Movement
The Linux systems (NIX01 and NIX02) often represent internal infrastructure.
These machines might:
- Run background services
- Support application logic
- Be used in CI/CD pipelines
If access is gained here, it suggests:
➡️ post-initial compromise activity
Key indicators to look for:
- SSH logins from unexpected sources
- Script execution tied to automation
- Credential reuse across systems
If TeamCity is involved, these systems become even more relevant.
Windows Systems: WIN01 & WIN02 HTB CJCA Luminex analysis
The Windows hosts:
- WIN01 (10.129.156.44)
- WIN02 (10.129.156.43)
are where user activity becomes more visible.
From a detection standpoint, focus on:
- Logon events
- Process creation
- Lateral movement patterns
If a user like john or marc suddenly authenticates across multiple systems, that’s worth investigating.
Also, watch for:
- Service account usage on user machines
- Cross-host authentication chains
These often indicate credential compromise.
ELK01: The Source of Truth
The ELK01 system is where everything comes together.
This is your visibility layer:
- Logs from web servers
- Authentication events
- System activity
But having logs isn’t enough—you need correlation.
For example:
- A suspicious request on WEB01
- Followed by login activity on NIX01
- Then authentication on WIN01
Individually, these might look harmless. Together, they form a pattern.
That’s the essence of CJCA analysis.
Building the Attack Narrative HTB CJCA Luminex analysis
When you connect the dots in the Luminex Ltd. scenario, a possible chain looks like this:
- Initial interaction with WEB01 (external access)
- Compromise or credential exposure
- Access to TeamCity using the teamcity account
- Execution of jobs affecting NIX01 / NIX02
- Credential reuse or lateral movement
- Activity observed on WIN01 / WIN02
- Logs aggregated and visible in ELK01
This isn’t a guaranteed path—but it reflects how multi-system environments behave under attack.
Common Mistakes in CJCA Labs
A few things tend to slow people down:
- Treating each host separately instead of correlating events
- Ignoring service accounts like teamcity
- Overlooking CI/CD systems as attack vectors
- Focusing only on alerts instead of raw logs
CJCA is less about “finding the exploit” and more about:
➡️ understanding behavior across systems
A More Effective Approach
If you’re stuck, try this:
- Start with a single suspicious event
- Trace it across systems
- Map user activity alongside it
- Identify where behavior deviates from normal
And most importantly:
Don’t rush to conclusions—build a timeline.
Final Thoughts
The HTB CJCA Luminex Ltd. scenario is designed to teach one core skill:
Correlation.
Systems like WEB01, NIX01, NIX02, WIN01, WIN02, combined with services like TeamCity and ELK01, create a realistic environment where no single log tells the full story.
Users like john, marc, cameron, sfisher, melissajenkins, kimkiara, and the teamcity account are just pieces of that story.
The real value comes from connecting them.
Vendor: https://academy.hackthebox.com/preview/certifications/htb-certified-junior-cybersecurity-associate
Buy This Dump: https://cyberservices.store/