HTB CWEE Guide: RoyalFlush, SecureData & Vitamedix Web Enumeration
The HTB CWEE web exploitation guide (Certified Web Exploitation Expert) path focuses on something many people underestimate: how small web application details turn into full compromise paths. In this scenario, targets like www.royalflush.htb, forum.royalflush.htb, securedata.htb, and vitamedix.htb are not isolated—they’re part of a connected web ecosystem.
At first glance, each looks like a separate application. But once you start digging, patterns begin to emerge.
Target Overview HTB CWEE web exploitation guide
- www.royalflush.htb → Main website (entry point)
- forum.royalflush.htb → Community/forum platform
- http://securedata.htb → Data handling / sensitive endpoint
- vitamedix.htb → Likely secondary application or partner service
This structure already suggests:
➡️ Subdomain relationships + shared backend logic
Starting Point: www.royalflush.htb
The main domain is where most users begin.
Typical focus areas:
- Authentication mechanisms
- Input fields (login, search, contact forms)
- Hidden endpoints or parameters
What matters here isn’t just finding a vulnerability—it’s understanding how the app behaves.
Look for:
- Inconsistent validation
- Reflected input
- Session handling issues
Because even small quirks often point to deeper problems.
forum.royalflush.htb: User Interaction = Attack Surface
Forums are naturally interactive, which makes them valuable.
On forum.royalflush.htb, pay attention to:
- User-generated content
- Profile fields
- Messaging systems
These often introduce:
- Stored input issues
- Injection points
- Privilege escalation through logic flaws
Sometimes, the vulnerability isn’t technical—it’s how roles are enforced.
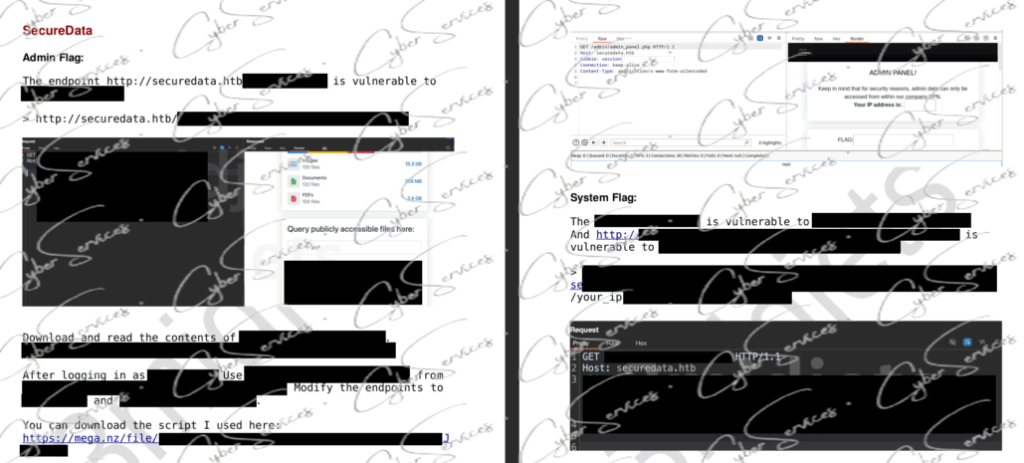
securedata.htb: Where Things Get Sensitive HTB CWEE web exploitation guide
The name securedata.htb is almost ironic.
Systems like this usually:
- Handle uploads or downloads
- Store sensitive information
- Require authentication
Key areas to explore:
- File handling functionality
- Access control checks
- Direct object references
If something is “secure,” it’s worth verifying how that security is actually implemented.
vitamedix.htb: The Overlooked Entry Point
Secondary domains like vitamedix.htb are often less hardened.
They may:
- Share authentication with the main app
- Reuse backend logic
- Contain older or unpatched code
Because of this, they can:
➡️ Provide easier entry than the main target
Check for:
- Outdated functionality
- Weak validation
- API endpoints
Connecting the Applications HTB CWEE web exploitation guide
The real challenge in CWEE isn’t finding a single issue—it’s chaining them.
For example:
- Identify input handling weakness on forum.royalflush.htb
- Use it to gain user-level access
- Reuse session or credentials on www.royalflush.htb
- Access restricted functionality on securedata.htb
- Pivot through vitamedix.htb for additional exposure
This kind of chaining is exactly what CWEE scenarios are built around.
Common Patterns to Watch HTB CWEE web exploitation guide
Across these targets, a few themes usually appear:
1. Shared Authentication
Multiple subdomains often trust the same session or token.
2. Inconsistent Validation
One app validates input properly, another doesn’t.
3. Access Control Gaps
Endpoints exist—but aren’t properly restricted.
4. Forgotten Features
Old or test functionality left accessible (especially on secondary domains).
Practical Approach
If you feel stuck, simplify your process:
- Map all endpoints first
- Test input behavior consistently
- Compare how each domain handles the same action
- Look for differences—not similarities
Because those differences usually lead somewhere.
Common Mistakes HTB CWEE web exploitation guide
- Focusing only on the main domain
- Ignoring secondary apps like vitamedix.htb
- Testing inputs without context
- Not chaining vulnerabilities
CWEE isn’t about one bug—it’s about the path.
Final Thoughts HTB CWEE web exploitation guide
The HTB CWEE RoyalFlush scenario shows how modern web environments actually work:
- Multiple applications
- Shared logic
- Small inconsistencies
Targets like www.royalflush.htb, forum.royalflush.htb, securedata.htb, and vitamedix.htb are all part of the same system—even if they don’t look like it at first.
The key is simple:
➡️ Don’t treat them separately. Treat them as one ecosystem.
Vendor: https://academy.hackthebox.com/preview/certifications/htb-certified-web-exploitation-expert
Buy this dump: https://cyberservices.store/