OSWP Guide: WPA-PSK, WPA-Enterprise & Router Interface Analysis
The OSWP wireless security guide (Offensive Security Wireless Professional) path is less about “breaking Wi-Fi quickly” and more about understanding how different wireless security models behave in practice. In this scenario, you’re dealing with:
- WPA-PSK (Personal) network
- WPA-MGT (Enterprise) network
- http://192.168.1.1/ → Router / access point interface
Each one requires a slightly different mindset—and that’s where most people get stuck.
WPA-PSK (Personal): The Baseline Target OSWP wireless security guide
The WPA-PSK network is usually the starting point.
It relies on:
- A shared password
- 4-way handshake authentication
From an assessment perspective, the focus is simple:
➡️ Capture authentication data, then test password strength
What matters here isn’t just capturing traffic—it’s timing and positioning. Clients connecting or reconnecting are what generate useful data.
Common weaknesses:
- Weak or predictable passwords
- Reused credentials
- Default configurations
➡️ If the password is strong, this path usually stops here.
WPA-Enterprise (WPA-MGT): Identity Over Password
The WPA-MGT (Enterprise) network is a different story.
Instead of a shared password, it uses:
- Individual user authentication
- Backend systems (like RADIUS)
- Certificate or credential-based access
This changes the approach completely.
You’re no longer attacking a single password—you’re targeting:
- Authentication flow
- User trust
- Misconfigurations
Key observation points:
- How clients validate the network
- Whether certificate validation is enforced
- How credentials are handled
➡️ Enterprise networks often fail due to misconfiguration, not weak passwords.
http://192.168.1.1/: The Overlooked Entry Point
The router interface:
➡️ http://192.168.1.1/
is often ignored—but it shouldn’t be.
This panel typically controls:
- Wireless settings
- Network segmentation
- Authentication modes
If accessible, check for:
- Default credentials
- Weak authentication
- Misconfigured wireless settings
Because sometimes, instead of attacking the network:
➡️ You can reconfigure it
Comparing WPA-PSK vs WPA-Enterprise OSWP wireless security guide
The key difference is mindset:
- WPA-PSK → attack the password
- WPA-Enterprise → attack the authentication process
In real environments:
- PSK fails due to weak passwords
- Enterprise fails due to poor configuration
Understanding this difference is critical for OSWP.
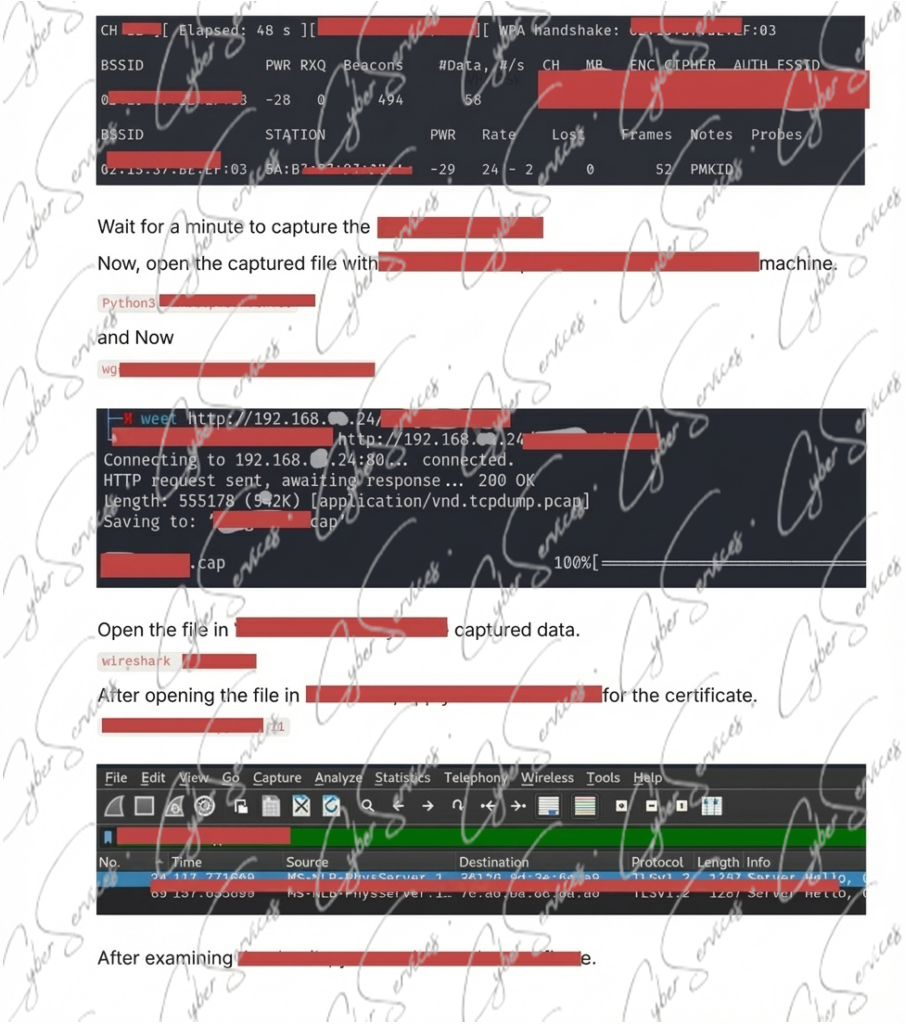
Practical Attack Flow
A realistic approach might look like:
- Identify WPA-PSK network
- Capture authentication traffic
- Test password strength
- Analyze WPA-Enterprise behavior
- Look for authentication weaknesses
- Access 192.168.1.1 if possible
- Review or abuse configuration
Common Mistakes OSWP wireless security guide
- Treating WPA-Enterprise like WPA-PSK
- Ignoring router interfaces
- Focusing only on password attacks
- Missing misconfiguration opportunities
Final Insight OSWP wireless security guide
The OSWP scenario highlights a simple truth:
➡️ Wireless security is only as strong as its weakest configuration
Between WPA-PSK, WPA-Enterprise, and the router interface at 192.168.1.1, the real opportunity isn’t always where you expect it.
Vendor: https://www.offsec.com/courses/pen-210/
Buy this dump: https://cyberservices.store/