PNPT Guide: The Pasta Mentors Network (External → Internal Pivot)
The TCM Security PNPT internal pivoting guide (Practical Network Penetration Tester) exam is built around one realistic idea: you start from the outside and work your way in. The thepastamentors.com scenario reflects that perfectly, combining an external network, an internal subnet, and just enough user context to build a full attack chain.
You’re dealing with:
- External: 10.10.10.0/24
- Internal: 10.10.155.0/24
- Domain: thepastamentors.com
- Users: [email protected], [email protected]
At first glance, it’s simple. But the connection between these elements is where the real progress happens.
External Network: 10.10.10.0/24 PNPT internal pivoting guide
This is your starting point.
From here, your goal is:
- Identify exposed services
- Enumerate web applications
- Discover entry points
Focus areas:
- Web servers
- Login panels
- Email-related services
The domain:
➡️ thepastamentors.com
is central to everything. It often ties together:
- Email accounts
- Web authentication
- Internal access
User Enumeration: Small Details Matter
You’re given two users:
Notice the second one carefully.
➡️ thepastamnetors.com (typo)
This is not random.
In PNPT-style scenarios, this can indicate:
- Typo-based misconfiguration
- Alternate domain usage
- Email-based attack surface
This is where:
- Username enumeration
- Password guessing patterns
- Email-based access
start to become relevant.
Initial Access: External Foothold PNPT internal pivoting guide
Typical entry points include:
- Web application vulnerabilities
- Weak authentication
- Credential reuse
Once you gain access, even limited:
➡️ Your objective shifts immediately to internal access
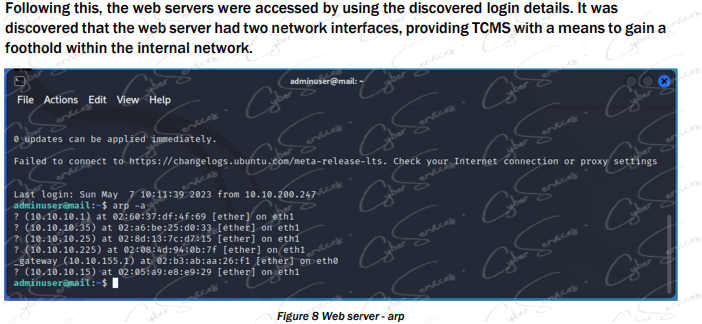
Internal Network: 10.10.155.0/24
After foothold, you pivot into:
➡️ 10.10.155.0/24
This network usually contains:
- Workstations
- Internal services
- Domain infrastructure
At this stage, focus on:
- Network discovery
- Credential harvesting
- Lateral movement
Pivoting: The Core of PNPT
This is where PNPT differs from simpler exams.
You’re expected to:
- Move from external → internal
- Maintain access
- Expand visibility
Common paths:
- Reuse credentials found externally
- Access internal services
- Move between hosts
➡️ Pivoting is not optional—it’s the main objective.
Credential Strategy PNPT internal pivoting guide
With users like:
- leo
- ferruccio
you should test:
- Password reuse across services
- Variations based on company naming
- Access across both networks
Also consider:
- Credentials exposed in web apps
- Config files
- Internal shares
Building the Attack Chain
A realistic flow might look like:
- Enumerate thepastamentors.com
- Identify login or exposed service
- Test users (leo / ferruccio)
- Gain initial access on external host
- Pivot into 10.10.155.0/24
- Enumerate internal systems
- Harvest credentials
- Move laterally across network
Common Mistakes PNPT internal pivoting guide
- Ignoring domain/email relationships
- Missing typos like thepastamnetors.com
- Staying too long on external network
- Not pivoting early enough
Practical Insight
One subtle but important theme here:
➡️ Identity is the bridge between networks
The same users (leo, ferruccio) often exist:
- Externally (web/email)
- Internally (AD / systems)
If you understand how identity flows, pivoting becomes much easier.
Final Thoughts
The PNPT The Pasta Mentors scenario is less about finding one vulnerability and more about building a path:
- External access
- User context
- Internal pivot
- Lateral movement
Everything—from thepastamentors.com to the internal 10.10.155.0/24 network—connects through small details.
And those small details are where success usually starts.
Vendor: https://certifications.tcm-sec.com/pnpt/
Buy this dump: https://cyberservices.store/