Why eWPT Certification Still Matters eWPT certification exam dump
For anyone eWPT certification exam dump trying to break into web application security, the eWPT certification is still one of the most practical entry-level certifications available. The biggest reason is simple: it focuses on realistic web penetration testing workflows instead of pure memorization.
A lot of certifications teach theory first and practice second. eWPT takes a different route. You are expected to understand reconnaissance, analyze web services, identify attack surfaces, and interpret how applications behave in real environments.
That difference matters.
Modern web pentesting is no longer about running random tools and hoping for an exploit. Strong reconnaissance and proper enumeration are usually what separate experienced testers from beginners.
Key areas commonly tested during eWPT preparation include:
- Information gathering
- Web application reconnaissance
- Subdomain discovery
- Port enumeration
- Authentication testing
- Directory enumeration
- HTTP response analysis
- Web exploitation fundamentals
These are practical skills used in real-world penetration testing engagements every day.
Understanding the Recon Phase in Web Pentesting
Many beginners spend too much time searching for exploits while ignoring reconnaissance. In reality, experienced penetration testers usually gain their biggest advantage during the enumeration phase.
Consider a target structure like this:
- http://infra.nexustech.com/
- http://infra.nexustech.com:8000/
- http://cms.nexustech.com/
- http://nexustech.com/
At first glance, these may look like ordinary web applications. But from a pentester’s perspective, they immediately suggest a larger attack surface.
Different subdomains and ports often indicate:
- Separate applications
- Internal administration panels
- Development environments
- API services
- Reverse proxies
- Misconfigured dashboards
- Legacy systems
This type of infrastructure is extremely common in both real penetration tests and eWPT-style labs.
Why Subdomains Matter During Enumeration
A domain like cms.nexustech.com may behave completely differently from infra.nexustech.com.
Even if both belong to the same company, they may run:
- Different frameworks
- Different authentication systems
- Different backend technologies
- Different security policies
For example:
- The CMS could be outdated and vulnerable
- The infrastructure panel might expose internal services
- One subdomain may sit behind a CDN while another reveals the origin server directly
Recognizing these differences is part of developing a real penetration testing mindset.
Analyzing Non-Standard Web Ports
One of the most common mistakes beginners make is only checking ports 80 and 443.
In modern environments, many applications run on alternative ports.
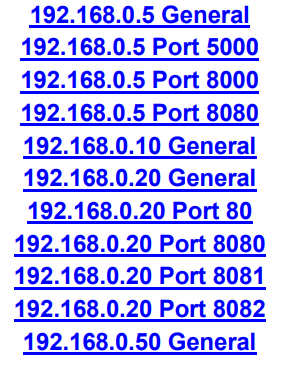
Examples from the provided infrastructure:
http://infra.nexustech.com:8000/192.168.0.5 Port 5000192.168.0.5 Port 8000192.168.0.5 Port 8080192.168.0.20 Port 80192.168.0.20 Port 8080192.168.0.20 Port 8081192.168.0.20 Port 8082
Ports like 5000, 8000, 8080, 8081, and 8082 often reveal:
- Flask applications
- Node.js services
- Admin dashboards
- Debug interfaces
- Development environments
- Internal APIs
- Jenkins or Grafana instances
- Reverse proxy configurations
For experienced testers, these ports immediately deserve extra attention.
What the Internal IP Structure Suggests eWPT certification exam dump
The screenshot also reveals multiple internal hosts:
- 192.168.0.5 General
- 192.168.0.10 General
- 192.168.0.20 General
- 192.168.0.50 General
This type of segmentation usually indicates multiple services operating inside the same environment.
192.168.0.5
This host exposes several services:
- 5000
- 8000
- 8080
That often points toward containerized applications or development stacks.
Many Flask and Node.js environments default to ports like these.
192.168.0.20
This system exposes:
- 80
- 8080
- 8081
- 8082
A setup like this frequently indicates:
- Multiple applications
- Reverse proxy routing
- Internal dashboards
- Staging environments
- Separate authentication systems
A skilled penetration tester would analyze each service independently.
That includes:
- HTTP headers
- Redirect behavior
- Login responses
- Cookie handling
- Framework fingerprints
- Session management
- Error messages
Enumeration is not just about discovering open ports. It is about understanding how every service behaves.
Useful Tools for eWPT Certification Preparation eWPT certification exam dump
Nmap
Still one of the most important tools for service discovery.
nmap -sV-Pn infra.nexustech.com
FFUF
Excellent for content discovery and endpoint fuzzing.
(command) BUY NOW http://cms.nexustech.com
(command) BUY NOW
Essential for:
- HTTP analysis
- Authentication testing
- Request manipulation
- Session analysis
(command) BUY NOW
Useful for identifying frameworks and backend technologies.
(command) BUY NOW http://nexustech.com
Common Mistakes During eWPT Preparation eWPT certification exam dump
Focusing Only on Exploitation
Real penetration testing starts long before exploitation.
The best testers first understand the application.
Weak Enumeration
Many vulnerabilities are hidden behind:
- Forgotten subdomains
- Misconfigured admin panels
- Alternative ports
- Debug interfaces
Skipping enumeration usually means missing critical findings.
Ignoring HTTP Responses eWPT certification exam dump
Some beginners only look at status codes.
Experienced testers analyze:
- Response length
- Redirect chains
- Cache headers
- Set-Cookie behavior
- Server fingerprints
- Authentication flow differences
Small inconsistencies often reveal valuable information.
How eWPT Skills Translate to Real-World Pentesting
The eWPT certification helps build the exact mindset companies look for in junior web pentesters.
Organizations increasingly value candidates who can:
- Perform reconnaissance effectively
- Understand HTTP behavior
- Analyze authentication systems
- Enumerate web applications manually
- Identify attack surfaces
- Think critically during testing
This is why methodology matters more than blindly using tools.
When experienced testers see targets like:
- http://infra.nexustech.com/
- http://infra.nexustech.com:8000/
- http://cms.nexustech.com/
- http://nexustech.com/
They immediately begin asking questions:
- Which services are public-facing?
- Which applications were meant for internal use?
- Is there a staging environment exposed externally?
- Are authentication responses consistent?
- Is a reverse proxy involved?
- Are backend technologies leaking through headers?
- Are there hidden admin interfaces?
That thought process is what real web pentesting looks like.
Final Thoughts eWPT certification exam dump
The eWPT certification is more than just another ethical hacking credential.
When approached correctly, it builds a strong foundation in:
- Web application reconnaissance
- Enumeration methodology
- HTTP analysis
- Service fingerprinting
- Practical web penetration testing
Modern infrastructures are complex.
A single company may expose:
- Multiple subdomains
- Several web applications
- Internal dashboards
- APIs
- Development services
- Reverse proxies
That is exactly why understanding targets like:
- infra.nexustech.com
- cms.nexustech.com
- nexustech.com
- 192.168.0.5
- 192.168.0.20
is valuable for anyone preparing for web penetration testing roles.
The strongest pentesters are rarely the ones who rush into exploitation first.
They are usually the ones who perform the best reconnaissance.
Vendor: https://ine.com/security/certifications/ewpt-certification
Buy this dump: https://cyberservices.store/
