CRTE Guide: Citadel & Glacis Domains – Active Directory and SQL Server Attack Path
The CRTE Active Directory guide (Certified Red Team Expert) exam environment is designed to feel like a real enterprise—messy, interconnected, and full of small misconfigurations that only make sense once you start linking them together.
In this scenario, you’re dealing with two domains:
- CITADEL.CORP
- GLACIS.CORP
Along with systems like CITADEL-DC, SRV71, PAWSRV, SQLSRV3, and GLACIS-DC, plus users such as studentuser, sharemanager, sqlsrv3adm, and dbmaster.
At first, it looks like a lot. But once you break it down, patterns start to emerge.
Environment Overview: Two Domains, One Opportunity
The infrastructure is split across:
CITADEL Domain
- ExamVM.CITADEL.CORP → Your starting point
- SRV71.CITADEL.CORP → Likely application or file server
- PAWSRV.CITADEL.CORP → Privileged Access Workstation (high-value)
- CITADEL-DC.CITADEL.CORP → Domain Controller
GLACIS Domain
- SQLSRV3.GLACIS.CORP → SQL Server system
- GLACIS-DC.GLACIS.CORP → Domain Controller
Right away, the presence of two domains suggests:
➡️ Trust relationships or cross-domain access paths
And that’s where CRTE scenarios usually get interesting.
Initial Access: studentuser and ExamVM
You typically begin with access as:
- Username: studentuser
This is your foothold.
From here, the focus should be:
- Enumerating domain structure
- Identifying accessible resources
- Mapping reachable systems
At this stage, it’s less about privilege—and more about visibility.
sharemanager: A Small Clue with Big Implications CRTE Active Directory guide
Another key account:
- Username: sharemanager
- Password: “Us3dForControllingFilesAcrossCitadel!”
Even the password tells a story.
It suggests:
- File-sharing responsibilities
- Possible access to shared drives or SMB resources
- Cross-system file control
This account is likely tied to:
- SRV71
- Shared folders across CITADEL.CORP
And that makes it valuable.
Because shared resources often contain:
- Scripts
- Credentials
- Configuration files
SRV71 & File Share Enumeration
With sharemanager, one of the first logical steps is exploring:
➡️ SRV71.CITADEL.CORP
File servers are often overlooked—but they frequently expose:
- Deployment scripts
- Backup files
- Hardcoded credentials
Look for:
- Unusual file naming patterns
- Config files referencing other systems
- Credentials reused across domains
Sometimes, the path forward isn’t an exploit—it’s a forgotten file.
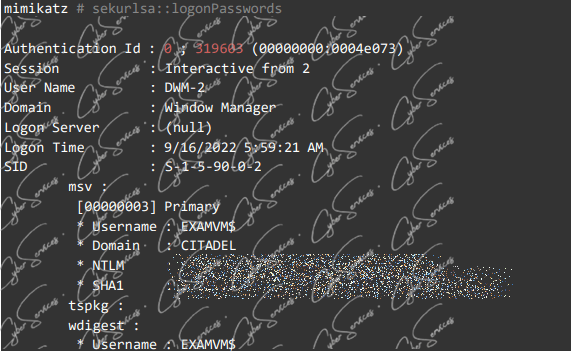
PAWSRV: Privileged Access Workstation CRTE Active Directory guide
The presence of PAWSRV.CITADEL.CORP is a major hint.
PAWs (Privileged Access Workstations) are used by admins to:
- Manage domain controllers
- Perform sensitive operations
If you gain access here, you’re not just moving laterally—you’re stepping into a privileged zone.
Key things to check:
- Logged-in users
- Credential artifacts
- Cached sessions
Because admin activity often leaves traces.
SQLSRV3.GLACIS.CORP: The Bridge Between Domains
Now things shift toward the GLACIS.CORP domain.
The system:
- SQLSRV3.GLACIS.CORP
along with users:
- sqlsrv3adm
- dbmaster
suggests a SQL-heavy environment.
SQL Servers are powerful because they often:
- Store credentials
- Interact with multiple systems
- Run under privileged service accounts
And importantly:
➡️ They can act as a bridge between domains
SQL Accounts: sqlsrv3adm and dbmaster
Accounts like:
- sqlsrv3adm
- dbmaster
are not just database users—they often have:
- System-level privileges
- Access to linked servers
- Execution capabilities (xp_cmdshell, etc.)
If access is gained here, possibilities include:
- Command execution on the SQL server
- Credential extraction
- Pivoting into the GLACIS domain
This is where AD meets database exploitation.
GLACIS-DC: The Final Target
The system:
- GLACIS-DC.GLACIS.CORP
represents the highest level of control in the second domain.
Reaching this point usually requires:
- Credential escalation
- Cross-domain movement
- Abuse of trust relationships
At this stage, the focus shifts from access to dominance.
Connecting the Attack Path CRTE Active Directory guide
When you step back, a realistic chain might look like this:
- Initial access via studentuser on ExamVM
- Discovery of sharemanager credentials
- Enumeration of SRV71 file shares
- Extraction of useful data or credentials
- Movement toward privileged systems like PAWSRV
- Discovery of SQL-related access
- Authentication to SQLSRV3.GLACIS.CORP using
sqlsrv3admordbmaster - Command execution or credential harvesting via SQL
- Pivot into GLACIS-DC
It’s not a straight line—but each step builds on the last.
Common Pitfalls in CRTE Scenarios CRTE Active Directory guide
Even experienced users get stuck here.
Typical mistakes include:
- Ignoring file shares (SRV71)
- Underestimating SQL Server access
- Treating domains as isolated
- Not analyzing password context (like sharemanager’s)
CRTE rewards patience and correlation—not speed.
A More Effective Strategy
If things aren’t moving forward, try this:
- Revisit file shares with fresh context
- Map relationships between accounts and systems
- Treat SQL as an entry point, not just a target
- Think in terms of access chains, not single steps
And always ask:
➡️ “Why does this account exist?”
That question alone often reveals the next move.
Final Thoughts CRTE Active Directory guide
The CRTE Citadel & Glacis scenario reflects how real enterprise environments operate:
- Multiple domains with hidden trust paths
- Service and management accounts with excessive access
- File shares and SQL systems acting as pivot points
Systems like SRV71, PAWSRV, SQLSRV3, and domain controllers like CITADEL-DC and GLACIS-DC, combined with users such as studentuser, sharemanager, sqlsrv3adm, and dbmaster, form a layered challenge.
The goal isn’t just to gain access.
It’s to understand how everything connects—and use that understanding to move forward.
Vendor: https://www.alteredsecurity.com/redteamlab
Buy this dump: https://cyberservices.store/