CRTM Guide: GCBTECH & GCBINFRA Active Directory Attack Path
The CRTM Active Directory guide (Certified Red Team Master) labs are designed to simulate real enterprise environments where nothing is isolated. The GCBTECH and GCBINFRA domains are a perfect example—multiple systems, overlapping access, and small misconfigurations that only make sense once you connect them.
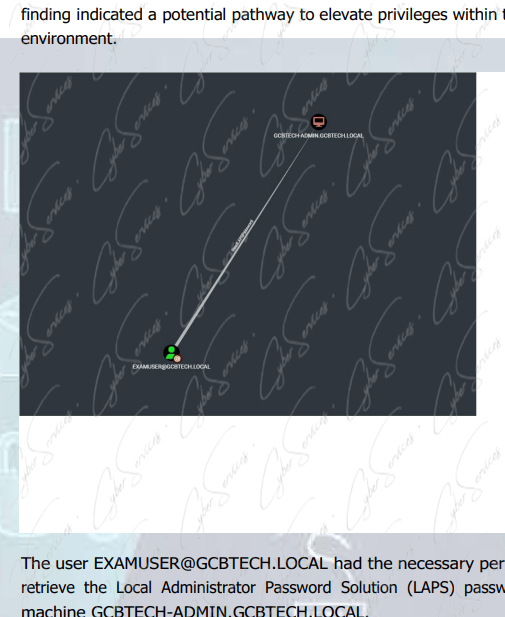
At first, hosts like GCBTECH-ADMIN, GCBTECH-SQL, GCBTECH-DC and GCBINFRA-DC, GCBINFRA-FILE look separate. In reality, they’re part of the same attack surface.
Environment Overview CRTM Active Directory guide
GCBTECH.LOCAL
- GCBTECH-ADMIN.GCBTECH.LOCAL → Admin system / workstation
- GCBTECH-SQL.GCBTECH.LOCAL → SQL Server (critical pivot point)
- GCBTECH-DC → Domain Controller
GCBINFRA.LOCAL
- GCBINFRA-DC.GCBINFRA.LOCAL → Domain Controller
- GCBINFRA-FILE.GCBINFRA.LOCAL → File server
- GCBINFRA-DC → Core AD system
This setup immediately suggests one thing:
➡️ Cross-domain movement is expected
Key Accounts to Focus On
- GCBTECH-ADMIN$ → Machine account (often underestimated)
- TECHADMIN → High-privileged administrative user
- filserveradmin → File server account (likely misconfigured)
Each of these opens a different path:
- File access
- Privilege escalation
- Lateral movement
Where to Start: Practical Entry Points
In CRTM scenarios, you don’t want to waste time guessing.
Two systems usually give the fastest results:
- GCBINFRA-FILE
- GCBTECH-SQL
Because:
- File servers leak credentials
- SQL servers execute commands
GCBINFRA-FILE: The Low-Hanging Fruit
File servers are rarely clean.
On GCBINFRA-FILE, you’ll typically find:
- Configuration files
- Scripts (.ps1, .xml, .config)
- Backup data
The account filserveradmin is key here.
Focus on:
- SMB shares
- Stored credentials
- Internal scripts referencing other systems
➡️ In many CRTM paths, this is where everything starts.
GCBTECH-SQL: The Real Pivot Point CRTM Active Directory guide
The system:
➡️ GCBTECH-SQL.GCBTECH.LOCAL
is one of the most valuable assets.
SQL Servers often:
- Run with high privileges
- Connect to multiple systems
- Allow command execution
If you gain access, check for:
- Command execution capabilities
- Stored credentials
- Linked servers
➡️ SQL is not just a database—it’s a bridge.
GCBTECH-ADMIN$: The Overlooked Account
The machine account:
➡️ GCBTECH-ADMIN$
is easy to ignore—but shouldn’t be.
In many cases, it can be used for:
- Kerberos-based attacks
- Delegation abuse
- Lateral movement
CRTM scenarios often include these intentionally.
TECHADMIN: The End Goal CRTM Active Directory guide
The account:
➡️ TECHADMIN
is likely:
- Domain admin
- Or very close to it
You usually won’t reach it directly.
Instead, access comes from:
- Credential reuse
- File share leaks
- SQL-based escalation
Cross-Domain Movement: The Core Challenge
The most important part of this scenario is:
➡️ GCBTECH ↔ GCBINFRA relationship
Look for:
- Shared credentials across domains
- Trust relationships
- File server data referencing another domain
CRTM isn’t about one domain—it’s about moving between them.
Example Attack Chain (Clean & Realistic) CRTM Active Directory guide
- Enumerate GCBINFRA-FILE
- Extract credentials via filserveradmin
- Pivot into GCBTECH-SQL
- Execute commands via SQL access
- Dump credentials
- Access TECHADMIN
- Move to Domain Controller
Common Mistakes
- Ignoring file servers
- Treating SQL as “just a database”
- Skipping machine accounts
- Not correlating domains
Final Insight
The CRTM GCBTECH & GCBINFRA scenario tests one core skill:
➡️ Can you connect small pieces into a full attack path?
Systems like GCBINFRA-FILE, GCBTECH-SQL, and accounts like filserveradmin, GCBTECH-ADMIN$, and TECHADMIN are not isolated.
They are steps in the same chain.
Vendor: https://www.alteredsecurity.com/gcb
Buy this dump: https://cyberservices.store/