CRTO Guide: Cobalt Strike Arsenal Kit & Dublin–London Infrastructure Attack Path
The CRTO Cobalt Strike guide (Certified Red Team Operator) labs are all about execution. You’re not just identifying weaknesses—you’re actively operating inside a network, moving step by step while trying to stay quiet.
In this scenario, the environment spans multiple segments and regions, including dublin.contoso.com and encrypted/internal zones like ENC. Combined with tools like the Cobalt Strike Arsenal Kit, it creates a workflow that feels very close to a real engagement.
Environment Overview CRTO Cobalt Strike guide
Dublin Domain (dublin.contoso.com)
- DUB-WKSTN-1 → User workstation
- DUB-WKSTN-2 → Another endpoint (often initial foothold)
- DUB-WEB-1 → Web server
- DUB-SQL-1 → Database server
- DUB-DC-1 → Domain Controller
London / Other Segments
- LON-DC-1 → Secondary Domain Controller
- ENC-JMP-1 → Jump server (restricted access zone)
- ENC-FS-1 → File server (likely sensitive data)
This layout immediately suggests:
➡️ Segmentation + lateral movement + pivoting
Initial Access: DUB-WKSTN-2
In most CRTO paths, the starting point is:
➡️ DUB-WKSTN-2
This is typically where your beacon lands.
At this stage, focus on:
- User context
- Network visibility
- Local privilege escalation opportunities
Don’t rush. Stability matters more than speed here.
Cobalt Strike Arsenal Kit: Why It Matters CRTO Cobalt Strike guide
The path:
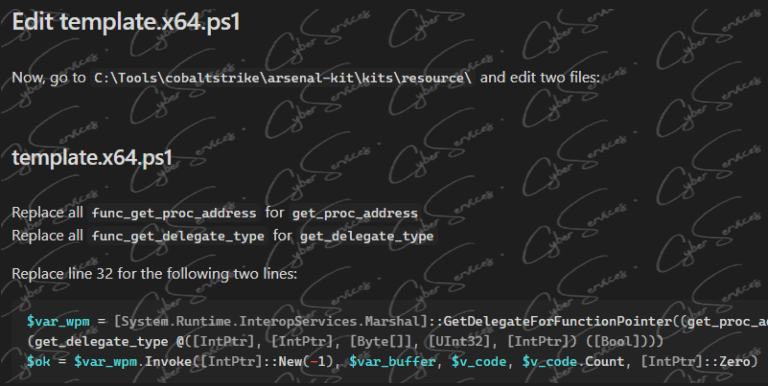
➡️ cobaltstrike\arsenal-kit\kits\artifact\src-common\
isn’t just a folder—it’s a core part of evasion.
The Arsenal Kit is used to:
- Customize payloads
- Modify artifacts (EXE/DLL)
- Bypass detection mechanisms
In real operations, default payloads get caught quickly.
Using Arsenal Kit allows you to:
- Change signatures
- Adjust memory behavior
- Blend into the environment
➡️ In CRTO, this is often the difference between success and getting flagged.
Expanding Access: From Workstation to Web & SQL CRTO Cobalt Strike guide
After foothold on DUB-WKSTN-2, the next logical steps include:
DUB-WKSTN-1
- Check for credential reuse
- Look for lateral movement opportunities
- Identify logged-in users
DUB-WEB-1
- Web servers often store credentials
- Config files may expose connection strings
- Useful for pivoting into backend systems
DUB-SQL-1
- High-value system
- Often allows command execution
- Can expose service account credentials
➡️ SQL servers frequently become pivot points in CRTO labs.
Privilege Escalation & Credential Access CRTO Cobalt Strike guide
Once you have multiple footholds, your focus shifts to:
- Credential dumping
- Token impersonation
- Service account abuse
These techniques help you move from:
➡️ Local access → Domain-level access
Pay attention to:
- Reused credentials across hosts
- Admin logins on workstations
- Service accounts running on SQL or web servers
Domain Controller: DUB-DC-1 CRTO Cobalt Strike guide
The system:
➡️ DUB-DC-1
is your primary objective in the Dublin domain.
Reaching it usually involves:
- Lateral movement
- Credential escalation
- Careful use of your beacon
Once access is achieved, you effectively control:
- Authentication
- Domain policies
- User management
Cross-Domain Movement: LON-DC-1
The presence of:
➡️ LON-DC-1
indicates another domain or a trusted environment.
At this stage, look for:
- Trust relationships
- Shared credentials
- Cross-domain authentication
CRTO scenarios often expect:
➡️ Pivoting beyond the initial domain
Restricted Segment: ENC Environment
Systems like:
- ENC-JMP-1
- ENC-FS-1
represent a more secure zone.
Access usually requires:
- Valid credentials
- Pivoting through a jump server
- Network tunneling
ENC-JMP-1
- Acts as a gateway
- Often heavily monitored
ENC-FS-1
- Likely contains sensitive files
- May hold credentials or internal data
➡️ This is where stealth becomes critical.
Example Attack Flow CRTO Cobalt Strike guide
A realistic path through this environment might look like:
- Initial beacon on DUB-WKSTN-2
- Lateral movement to DUB-WKSTN-1
- Credential discovery on DUB-WEB-1
- Pivot to DUB-SQL-1 for command execution
- Privilege escalation and credential dumping
- Access to DUB-DC-1
- Identify trust → move to LON-DC-1
- Pivot into ENC-JMP-1
- Access sensitive data on ENC-FS-1
Common Mistakes in CRTO
- Using default payloads (detected quickly)
- Moving too fast and losing access
- Ignoring segmentation
- Not using Arsenal Kit effectively
CRTO is about control—not noise.
Practical Tips CRTO Cobalt Strike guide
- Modify payloads early using Arsenal Kit
- Keep your beacon stable
- Move only when necessary
- Always think one step ahead
Final Thoughts
The CRTO Dublin–London scenario highlights a key reality:
➡️ Modern networks are segmented—but still connected.
Systems like DUB-WKSTN-2, DUB-SQL-1, DUB-DC-1, LON-DC-1, and restricted assets like ENC-JMP-1 and ENC-FS-1 are all part of a single chain.
With tools like the Cobalt Strike Arsenal Kit, your job isn’t just to gain access—
It’s to stay undetected while moving forward.
Vendor: https://www.zeropointsecurity.co.uk/course/red-team-ops
Buy this dump: https://cyberservices.store/