HTB CPTS Guide: Trilocor Robotics Active Directory & Web Enumeration
When you dive into the HTB CPTS Trilocor guide (Certified Penetration Testing Specialist) path, scenarios start to feel much closer to real corporate environments. The Trilocor Robotics lab is a great example of that balance—Active Directory, internal services, and just enough misconfiguration to reward careful thinking.
At first glance, names like rhinkle, dev_user1, ….. buy this dump, ….. buy this dump, ….. buy this dump, and hosts such as prototype-beta.trilocor.local or gogs-qa0001.trilocor.local may seem disconnected. But once you start mapping relationships, the structure becomes clearer.
Environment Overview: Trilocor.local Domain
The core of the lab is the Trilocor.local domain.
This environment includes:
- Multiple user accounts (standard, admin, service)
- Internal development systems
- Web applications tied to QA and testing
Right away, that mix suggests one thing:
➡️ Development and production boundaries may not be strictly enforced
And that’s usually where interesting paths appear.
User Landscape: Identifying High-Value Accounts HTB CPTS Trilocor guide
The domain includes a wide range of users:
- rhinkle
- dev_user1
- ….. buy this dump
And more privileged-looking accounts:
- fjenkins_adm
- ….. buy this dump
At a glance, you can already categorize them:
Standard Users
Accounts like rhinkle is likely entry points. These are often:
- Phishable
- Reused across services
- Less monitored
Administrative Accounts
Users ending with _adm or names like admin1 typically:
- Have elevated privileges
- Are used for system management
- May be over-permissioned
Service Accounts
The standout here is svc_adconnect.
This strongly suggests Azure AD Connect or directory synchronization, which often:
- Stores credentials
- Has replication privileges
- Becomes a critical escalation point if compromised
Initial Access: Where It Usually Begins HTB CPTS Trilocor guide
In environments like this, initial access rarely comes from admin accounts.
More likely paths include:
- Weak credentials on standard users
- Access to internal applications
- Exposed development systems
That’s where assets like:
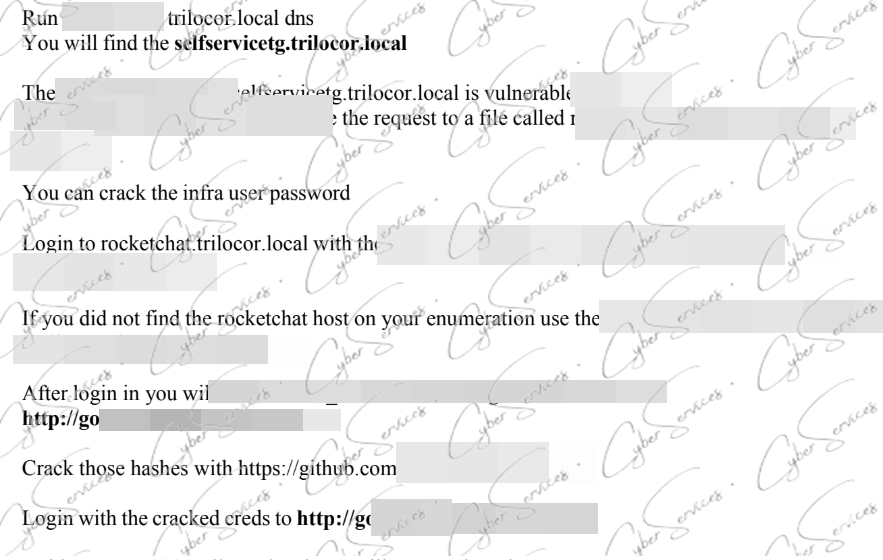
- prototype-beta.trilocor.local
- http://gogs-qa0001.trilocor.local/index.php
become important.
Gogs QA Instance: A Subtle Entry Point
The URL:
➡️ http://gogs-qa0001.trilocor.local/index.php
points to a Gogs (Git service) instance, likely used for development or QA.
These systems are often overlooked—but they can expose:
- Source code
- Credentials in config files
- API keys or tokens
If accessible, this should be one of the first places to check.
Look for:
- Hardcoded credentials
- Repository secrets
- User activity tied to accounts like
dev_user1
Because developers often leave traces unintentionally.
prototype-beta.trilocor.local: Testing Environments Are Risky
The prototype-beta host name says a lot.
“Prototype” and “beta” usually mean:
- Not fully secured
- Used for testing features
- Less strict access control
These environments often:
- Mirror production data
- Use shared credentials
- Skip security hardening
If you gain access here, it may reveal:
- Internal APIs
- Credentials reused in the main domain
- Connections to other systems
It’s not just another host—it’s a bridge.
Service Account Focus: svc_adconnect HTB CPTS Trilocor guide
Among all users, svc_adconnect deserves special attention.
In real environments, Azure AD Connect accounts:
- Have directory replication rights
- Can access sensitive AD data
- Are rarely rotated properly
If this account is accessible, potential paths include:
- Credential extraction
- Directory synchronization abuse
- Privilege escalation toward domain-level access
This is often where a mid-level foothold turns into full compromise.
Admin Accounts: fjenkins_adm, mvargas_adm, admin1
Accounts like:
- fjenkins_adm
- ….. buy this dump
represent the final stage of escalation.
But reaching them directly is unlikely.
Instead, look for:
- Credential reuse
- Access through service accounts
- Misconfigured permissions
Sometimes, these accounts don’t need to be “cracked”—they’re exposed indirectly through:
- Scripts
- Config files
- Automation tools
Mapping a Realistic Attack Path HTB CPTS Trilocor guide
When you connect everything, a potential flow might look like:
- Access gained via Gogs QA (gogs-qa0001)
- Discovery of credentials tied to
dev_user1or similar - Authentication into prototype-beta.trilocor.local
- Credential reuse or escalation to service accounts
- Access to ….. buy this dump
- Movement toward admin-level accounts like
fjenkins_admoradmin1
This isn’t a strict sequence—but it reflects how layered environments behave.
Common Mistakes in CPTS Labs
A few things tend to trip people up:
- Ignoring development systems like Gogs
- Treating all users equally
- Overlooking service accounts
- Not checking for credential reuse
CPTS scenarios reward prioritization—not brute force.
A More Practical Approach HTB CPTS Trilocor guide
If progress slows down, try shifting focus:
- Start with exposed services (like Gogs)
- Identify credential relationships
- Map user roles before attacking them
- Focus on “why this account exists”
Because context often matters more than the exploit itself.
Final Thoughts HTB CPTS Trilocor guide
The Trilocor Robotics CPTS scenario is a strong example of how modern environments actually look:
- Development and production overlap
- Service accounts hold hidden power
- Internal tools expose sensitive data
Users like rhinkle, accounts such as fjenkins_adm, along with systems like prototype-beta.trilocor.local and gogs-qa0001.trilocor.local, are all part of the same story.
The challenge isn’t finding them—it’s understanding how they connect.
Vendor: https://academy.hackthebox.com/preview/certifications/htb-certified-penetration-testing-specialist
Buy this dump: https://cyberservices.store/